Splunk – Creates real-time business impact from data
From dealing with security concerns to production monitoring, businesses need to analyze the log data of their systems to ensure everything is functioning normally. In a computing context, a log refers to automatically produced and time-stamped documentation of events related to a particular system. Analysis of log data helps businesses comply with regulations, security policies and audits, understand online consumer behavior, and comprehend system troubleshoots. Businesses need to review their system logs daily to search for errors, anomalies, or suspicious activity that deviates from the norm.
A platform that empowers businesses to monitor, analyze and act the right way
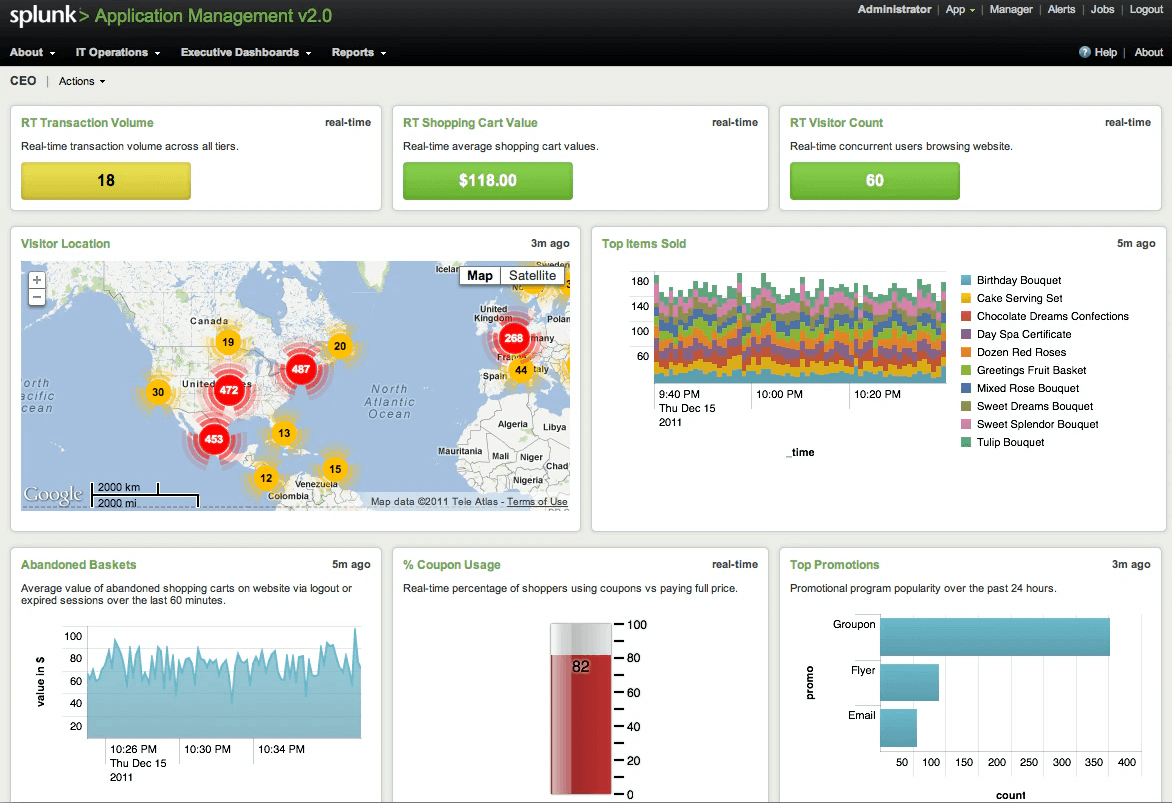
Splunk is an advanced data analytics tool for organizations that need to consolidate log data. This customizable log data analysis software provides you with an intelligent and efficient engine for machine data that helps businesses in monitoring, searching, analyzing, and visualizing large amounts of data. The software works and supports different technologies that extend its capabilities and use. Splunk is available in three versions – Enterprise, Light, and Cloud.
The log data analysis platform also offers a website monitoring app that can calculate website uptime and provide a historical analysis of the website’s responsiveness. The app can monitor the website and send an email alert when it is down. Splunk also provides a wide range of apps that provide rich functionality and critical resource management. The apps like PCI compliance, Splunk Analytics for Hadoop, DB Connect, Mobile Intelligence, UNIX, and Linux work with most data sources and provides the flexibility the user needs.
Features
Network Monitoring
Splunk offers complete network monitoring tools that allow you to monitor bandwidth, Internet usage, IP address, web traffic, SLA and performs network resource management more effectively.
Application Performance Management
It can perform trace individual transactions and perform full transaction diagnostics. The root-cause diagnosis allows the IT team to identify the root causes affecting server performance and fix it without any delays.
Log Management
It can monitor and analyze network logs, sys logs, and weblogs. Splunk can also perform audit trails that help in compliance reporting.
Machine Learning
The platform incorporates machine learning technologies that help it in deep learning and model training. It also features an advanced ML algorithm library and statistical/mathematical tools that help in predictive modeling.
How does it work?
Splunk has a multi-tier architecture and to understand its working, you should know its different components:
- Universal Forwarder – UF is a lightweight element and its main function is to push data to the heavy Splunk forwarder. UF just pushes log data to the server and it can be installed at the application side or client-side.
- Load Balancer – As the name suggests, the LB element distributes the network traffic over a cluster of servers.
- Heavy Forwarder – It is a heavy element with the primary function of filtering the log data. For example, HF can help accumulate only error logs.
- Indexer – The main function of the indexer is to store and index data. It implements indexing like date and time, sources, and hosts.
- Search Head – This is a Splunk instance that helps in distributions of searches to different indexers. The Search Head doesn’t have an instance of its own. It is primarily used to perform reporting and achieve intelligence.
- Deployment Master – As the name suggests, Splunk elements help in deploying the configuration of other elements like updating the Universal Forwarder. Deployment Master is also used to share data between the components.
A typical Splunk deployment is made of following components which may exist on a single machine:
- Forwarder
- Indexer
- Search Head
The Splunk Architecture’s Working In-Detail
Step 1 – The forwarder tracks the data, makes a copy of data, and performs load balancing on that particular data before sending it to the Indexer. Cloning helps in producing duplicate copies of cases at the data sources. One of the advantages of duplicating data is even if one case collapses during load balancing; the data can be carried to the case which is hosting the indexer.
Step 2 – The data obtained from the forwarder is dropped in the indexer component where it is split into various logical datastores.
Step 3 – The data inside the Indexer can be explored and you can assign explorations to different search companions. The results obtained after assigning are merged and carried forward to Search Head. You can schedule search companions and create alerts for different search scenarios. The alerts would be activated automatically when any situations match the saved searches.
Step 4 – In a distributed search environment, the Splunk (search head) instance handles search management functions and directs search requests to a set of search peers and merges the results back to the user. The search head and knowledge objects can be retrieved from Splunk Web Interface or Splunk CLI. The interaction occurs over a REST API connection.
Evaluating Splunk
Pros
- No database or services dependency
- Finds real-time logs faster
- Requires minimum hardware resource (cloud-based)
- Accept any data formats like CSV, JSON, and more
- Generates alerts and reports for log searches
Cons
- The multi-tier architecture makes the learning curve stiff. You need to spend lots of time learning the usage of the tool
- Log data searches are difficult to understand especially the search syntax and regular expressions
- The dashboard is not effective like other monitoring tools
- Proves expensive for analysis of large data volumes
Splunk – Advanced Data Analytics for Smart Organizations splunk.com/ via @supermonitoring
Final Word
Today, every activity that occurs online on smartphones, computers, tablets, and systems is logged somewhere in some form. Hence, employing a log analysis platform is now more crucial than ever before. With technology, threats expanding and becoming complex every day, you need log analysis software that can successfully navigate the ins and outs of the complex and puzzling logs that systems report back to us.
Splunk is a powerful log data analytical tool that makes log data access and analysis simple and fast due to advanced technology behind it. The software can work in diverse IT environments and analyze machine-generated data, unstructured/structured, and complex multi-line data efficiently by breaking the data into smaller parts and providing answers faster.